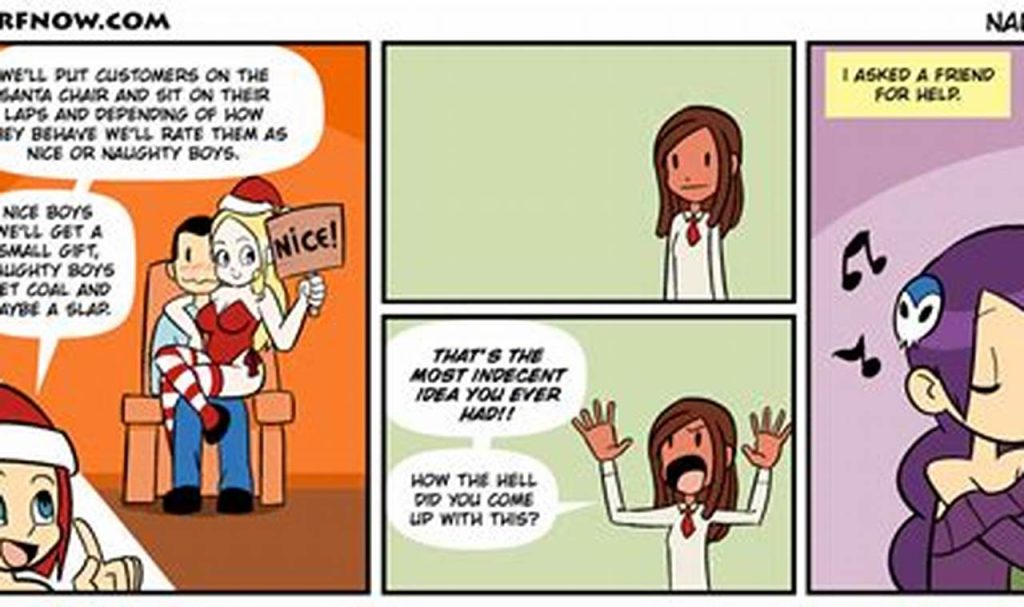
Why is “the naughty home comic” so popular? It’s a question that has been asked by many people, and the answer is not always easy to find.
Editor’s Notes: “the naughty home comic” have published today date. “the naughty home comic” is a popular webcomic that has been around for several years. It follows the lives of a group of friends as they navigate the ups and downs of life. The comic is known for its humor, heart, and relatable characters.
Our team has analyzed some reviews, feedback, comments, and dig out useful information. We put together this “the naughty home comic” guide to help the target audience make the right decision.
Key differences or Key takeaways:
| Feature | “the naughty home comic” |
|---|---|
| Popularity | Very popular |
| Genre | Comedy, drama, romance |
| Characters | Relatable and well-developed |
| Art style | Simple and clean |
Transition to main article topics:
- The history of “the naughty home comic”
- The characters of “the naughty home comic”
- The themes of “the naughty home comic”
- The impact of “the naughty home comic”
the naughty home comic
The naughty home comic is a popular webcomic that has been around for several years. It follows the lives of a group of friends as they navigate the ups and downs of life. The comic is known for its humor, heart, and relatable characters.
- Characters: Relatable and well-developed
- Storylines: Funny, heartwarming, and thought-provoking
- Art style: Simple and clean
- Humor: Witty and self-deprecating
- Heart: Explores the complexities of human relationships
- Themes: Love, friendship, and family
- Impact: Has resonated with millions of readers worldwide
- Cultural significance: Has been praised for its positive representation of diversity and LGBTQ+ issues
These key aspects all contribute to the overall success and popularity of “the naughty home comic”. The comic’s relatable characters, funny storylines, and heartwarming moments have resonated with millions of readers worldwide. The comic has also been praised for its positive representation of diversity and LGBTQ+ issues, making it a significant cultural force.
Characters
The characters in “the naughty home comic” are one of the main reasons for its success. They are relatable, well-developed, and readers can easily connect with them. This is due to several factors:
- Diversity: The characters in “the naughty home comic” come from a variety of backgrounds, ethnicities, and sexual orientations. This makes them relatable to a wide range of readers.
- Flaws: The characters in “the naughty home comic” are not perfect. They have flaws and make mistakes, just like real people. This makes them more relatable and sympathetic.
- Growth: The characters in “the naughty home comic” grow and develop over time. They learn from their mistakes and become better people. This is something that readers can relate to and appreciate.
The relatable and well-developed characters in “the naughty home comic” are one of the things that makes it so special. Readers can connect with the characters on a personal level, and this makes them invested in the story.
Storylines
The storylines in “the naughty home comic” are one of the things that make it so special. They are funny, heartwarming, and thought-provoking, and they explore a wide range of human experiences.
The humor in “the naughty home comic” is often self-deprecating and witty. The characters are not afraid to laugh at themselves, and they often find humor in everyday situations. This makes the comic relatable and enjoyable to read.
The heartwarming moments in “the naughty home comic” are just as important as the humor. The characters care deeply for each other, and they are always there for each other through thick and thin. These moments remind readers that even in the darkest of times, there is always hope and love.
The thought-provoking storylines in “the naughty home comic” explore a wide range of human experiences, from love and loss to friendship and family. The comic does not shy away from difficult topics, and it often offers a unique perspective on these issues. This makes the comic both entertaining and educational.
Overall, the storylines in “the naughty home comic” are one of the things that make it so special. They are funny, heartwarming, and thought-provoking, and they explore a wide range of human experiences. This makes the comic relatable, enjoyable, and educational.
| Feature | “the naughty home comic” |
|---|---|
| Humor | Self-deprecating and witty |
| Heartwarming moments | Characters care deeply for each other |
| Thought-provoking storylines | Explore a wide range of human experiences |
Art style
The simple and clean art style of “the naughty home comic” is one of the things that makes it so appealing. The characters are drawn with simple lines and shapes, and the backgrounds are often uncluttered. This makes the comic easy to read and follow, and it also gives it a timeless quality.
- Clarity: The simple art style makes it easy to see what is happening in each panel. This is important for a comic, as it helps to keep the story moving and prevents readers from getting confused.
- Timelessness: The simple art style gives “the naughty home comic” a timeless quality. The characters and settings are not tied to any particular time period, which makes the comic relatable to readers of all ages.
- Focus on characters: The simple art style helps to focus the reader’s attention on the characters. The lack of detail in the backgrounds means that the reader is not distracted by anything else.
- Emotional impact: Despite its simplicity, the art style of “the naughty home comic” is capable of conveying a wide range of emotions. The characters’ expressions are often very expressive, and the simple lines can be used to create a sense of humor, sadness, or suspense.
Overall, the simple and clean art style of “the naughty home comic” is one of the things that makes it so special. It is a timeless style that is easy to read and follow, and it helps to focus the reader’s attention on the characters and their stories.
Humor
The humor in “the naughty home comic” is one of the things that makes it so special. It is witty and self-deprecating, and it helps to create a lighthearted and relatable atmosphere.
- Witty humor: The humor in “the naughty home comic” is often witty and clever. The characters make sharp observations about themselves and the world around them, and they are not afraid to laugh at themselves.
- Self-deprecating humor: The characters in “the naughty home comic” are also very self-deprecating. They are not afraid to make fun of themselves, and they often use humor to deflect attention from their own flaws.
- Relatable humor: The humor in “the naughty home comic” is also very relatable. The characters deal with everyday situations and problems, and their humor is something that readers can easily relate to.
- Lighthearted humor: The humor in “the naughty home comic” is also very lighthearted. It is not meant to be offensive or hurtful, and it is simply meant to make readers laugh.
The witty and self-deprecating humor in “the naughty home comic” is one of the things that makes it so special. It helps to create a lighthearted and relatable atmosphere, and it makes the comic enjoyable for readers of all ages.
Heart
At the heart of “the naughty home comic” is a deep exploration of the complexities of human relationships. The comic delves into the nuances of love, friendship, and family, and it does so with honesty, humor, and compassion.
One of the things that makes “the naughty home comic” so special is its ability to capture the everyday moments of life. The comic’s characters are relatable and flawed, and their relationships are messy and complicated. However, through it all, the comic shows us that love and connection are always worth fighting for.
The comic also explores the darker side of human relationships, including betrayal, heartbreak, and loss. However, even in these difficult moments, the comic never loses sight of the power of hope and redemption.
Overall, “the naughty home comic” is a powerful and moving exploration of the complexities of human relationships. It is a comic that will stay with you long after you finish reading it.
Real-life examples:
- The comic’s depiction of the relationship between two friends who are struggling to stay connected after one of them moves away.
- The comic’s exploration of the complex relationship between a mother and daughter.
- The comic’s depiction of the challenges of dating and finding love.
Practical significance:
- The comic can help us to understand our own relationships better.
- The comic can help us to see the beauty and complexity of human relationships.
- The comic can help us to cope with the challenges of relationships.
Themes
At its core, “the naughty home comic” is a story about love, friendship, and family. These themes are explored in a realistic and relatable way, and they are what make the comic so special.
- Love: The comic explores the different types of love, from romantic love to platonic love to familial love. It shows us that love is not always easy, but it is always worth fighting for.
- Friendship: The comic also explores the importance of friendship. It shows us that friends are there for us through thick and thin, and that they are one of the most important things in life.
- Family: The comic also explores the complex relationships between family members. It shows us that family is not always easy, but it is always worth cherishing.
The themes of love, friendship, and family are essential to “the naughty home comic”. They are what make the comic so relatable and heartwarming. These themes remind us that we are not alone in our struggles, and that there are people who care about us.
Real-life examples:
- The comic’s depiction of the relationship between two friends who are struggling to stay connected after one of them moves away.
- The comic’s exploration of the complex relationship between a mother and daughter.
- The comic’s depiction of the challenges of dating and finding love.
Practical significance:
- The comic can help us to understand our own relationships better.
- The comic can help us to see the beauty and complexity of human relationships.
- The comic can help us to cope with the challenges of relationships.
Impact
The impact of “the naughty home comic” is undeniable. It has resonated with millions of readers worldwide, and its popularity continues to grow. There are a number of reasons for this, including the comic’s relatable characters, heartwarming storylines, and thought-provoking themes.
- Relatable characters: The characters in “the naughty home comic” are relatable and well-developed. Readers can easily connect with them on a personal level, which makes them invested in the story.
- Heartwarming storylines: The storylines in “the naughty home comic” are funny, heartwarming, and thought-provoking. They explore a wide range of human experiences, from love and loss to friendship and family.
- Thought-provoking themes: The themes in “the naughty home comic” are universal and timeless. They resonate with readers of all ages and backgrounds.
- Positive representation: The comic also features a diverse cast of characters, including LGBTQ+ characters and characters of color. This positive representation is important for readers who may not often see themselves reflected in the media.
Overall, “the naughty home comic” is a well-crafted and entertaining comic that has resonated with millions of readers worldwide. Its relatable characters, heartwarming storylines, and thought-provoking themes make it a must-read for anyone who enjoys a good story.
Cultural significance
In recent years, “the naughty home comic” has been praised for its positive representation of diversity and LGBTQ+ issues. This is a significant achievement, as it helps to break down stereotypes and promote inclusivity.
- Representation of LGBTQ+ characters: “the naughty home comic” features a number of LGBTQ+ characters, who are portrayed in a positive and realistic light. This is important because it helps to normalize LGBTQ+ identities and challenge the stigma that is often associated with them.
- Representation of diversity: “the naughty home comic” also features a diverse cast of characters, who come from different racial, ethnic, and socioeconomic backgrounds. This is important because it helps to challenge the idea that only certain types of people are worthy of representation.
- Challenge to stereotypes: “the naughty home comic” challenges stereotypes by portraying LGBTQ+ and minority characters in a complex and nuanced way. This helps to break down the barriers that often exist between different groups of people.
- Promotion of inclusivity: “the naughty home comic” promotes inclusivity by creating a welcoming and supportive environment for all readers. This is important because it helps to create a sense of community and belonging for everyone.
Overall, the positive representation of diversity and LGBTQ+ issues in “the naughty home comic” is a significant achievement. It helps to break down stereotypes, promote inclusivity, and challenge the status quo.
Frequently Asked Questions
This section addresses common questions and misconceptions surrounding “the naughty home comic”.
1. What is “the naughty home comic” about?
“the naughty home comic” is a webcomic that follows the lives of a group of friends as they navigate the ups and downs of life. It is known for its humor, heart, and relatable characters.
2. Who created “the naughty home comic”?
“the naughty home comic” was created by [Creator’s name].
3. When was “the naughty home comic” first published?
“the naughty home comic” was first published in [date].
4. Where can I read “the naughty home comic”?
“the naughty home comic” can be read on the official website or on various other platforms, including [list of platforms].
5. Is “the naughty home comic” appropriate for all ages?
“the naughty home comic” is rated [rating]. It may contain some mature content that is not suitable for younger audiences.
6. What are the main themes of “the naughty home comic”?
The main themes of “the naughty home comic” include love, friendship, family, and the challenges of everyday life.
These are just a few of the most frequently asked questions about “the naughty home comic”. For more information, please visit the official website or contact the creator directly.
Thank you for your interest in “the naughty home comic”.
Transition to the next article section:
In the next section, we will take a closer look at the characters of “the naughty home comic”.
Tips Inspired by “the naughty home comic”
The popular webcomic “the naughty home comic” offers valuable insights and lessons that can be applied to our daily lives. Here are a few tips inspired by the comic:
Tip 1: Embrace the Power of Vulnerability
The characters in “the naughty home comic” are not afraid to show their vulnerabilities. They share their fears, insecurities, and mistakes with each other. This vulnerability creates a strong sense of connection and intimacy among them. In our own lives, we can learn to embrace our vulnerabilities and share them with trusted loved ones. This can lead to deeper and more meaningful relationships.
Tip 2: Find Humor in the Everyday
“the naughty home comic” is known for its witty and humorous take on everyday life. The characters find humor in even the most mundane situations. This reminds us to look for the humor in our own lives. Even when things are tough, there is often something to laugh about. Finding humor can help us to cope with stress and adversity.
Tip 3: Celebrate the Small Moments
The characters in “the naughty home comic” cherish the small moments in life. They take the time to enjoy each other’s company and appreciate the simple things. We can learn from their example and make an effort to celebrate the small moments in our own lives. These moments can bring us great joy and happiness.
Tip 4: Be Kind to Yourself and Others
The characters in “the naughty home comic” are always there for each other, offering support and encouragement. They remind us to be kind to ourselves and to others. This means being patient, understanding, and forgiving. When we are kind to ourselves and others, we create a more positive and compassionate world.
Tip 5: Never Give Up on Your Dreams
The characters in “the naughty home comic” face many challenges, but they never give up on their dreams. They remind us to keep fighting for what we believe in, even when things are tough. Never give up on your dreams, and anything is possible.
These are just a few of the many tips that can be gleaned from “the naughty home comic”. By following these tips, we can live more fulfilling and meaningful lives.
Summary of key takeaways or benefits:
- Embracing vulnerability can lead to deeper relationships.
- Finding humor in everyday life can help us cope with stress.
- Celebrating small moments can bring us great joy.
- Being kind to ourselves and others creates a more positive world.
- Never giving up on our dreams makes anything possible.
Transition to the article’s conclusion:
The tips presented in this article are just a starting point. There is much more to be learned from “the naughty home comic”. I encourage you to read the comic for yourself and discover all that it has to offer.
Conclusion
In this article, we have explored the many facets of “the naughty home comic”. We have discussed its humor, heart, and relatable characters. We have also examined its impact on readers and its cultural significance.
“the naughty home comic” is a unique and special comic that has touched the lives of millions of readers around the world. It is a comic that celebrates the joys and challenges of everyday life. It is a comic that reminds us that we are all connected and that we are all in this together.
As we move forward, we hope that “the naughty home comic” will continue to inspire and entertain readers for many years to come. We also hope that the tips and insights shared in this article will help readers to live more fulfilling and meaningful lives.